Balanced Learning Design
“Intelligence plus character—that is the goal of true education.” – Dr. Martin Luther King Jr.
So Much This creates educational interventions blending modern neuroscience, developmental psychology, and digital technologies with perenial methods of developing wisdom. This is Whole Mind Learning, a balanced approach to building experiences people love.
Hard work is good for the soul
lead
Whether you need a single webinar, a weeklong in-person training, or a multi-month program overhaul from goal setting to strategy development, program design, change management, implementation, and assessment, So Much This can help lead the way.
research
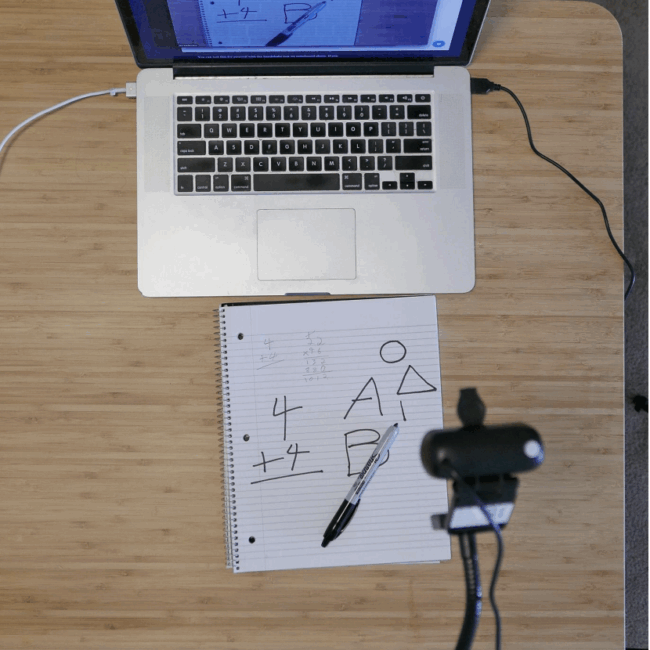
Focus groups, U/X in-depth interviewing, usability studies, survey design, outcome assessment, etc. for children through adults. Whether quick formative work or deep investigations for publication, findings will be jargon-free and easy to act on.
design
There is no such thing as “one size fits all” in learning design. I always start with the “Who?” and the “Why?” From there, the solution could be digital, analog, live, asynchronous, or any combination. Throughout the design process, co-creation is the key word.
develop
From rapidly iterated prototypes for formative research to complete online courses, LMS setup, and print materials, So Much This can make it. Solutions are delivered on time, under budget, and with longterm use in mind. Everything should be built to iterate.
deliver
Without thoughtful execution, attention to the learners in the moment, and the ability to adapt on the fly, the best designs and most innovative tools don’t work. Expertise in facilitation, lecture, train the trainer, and other delivery modalities.
evaluate
Each project has a different need and ability to invest in evaluation, but there’s always a way to tell if we’re on the right track. The right-size solution can always be found, and A So Much This project always ends with a clear idea of where to head next.